Adopting AI-driven tools for reviews and automation. This post examines how cloud-focused plugins can be combined with existing tooling to perform semi-autonomous cloud security reviews.
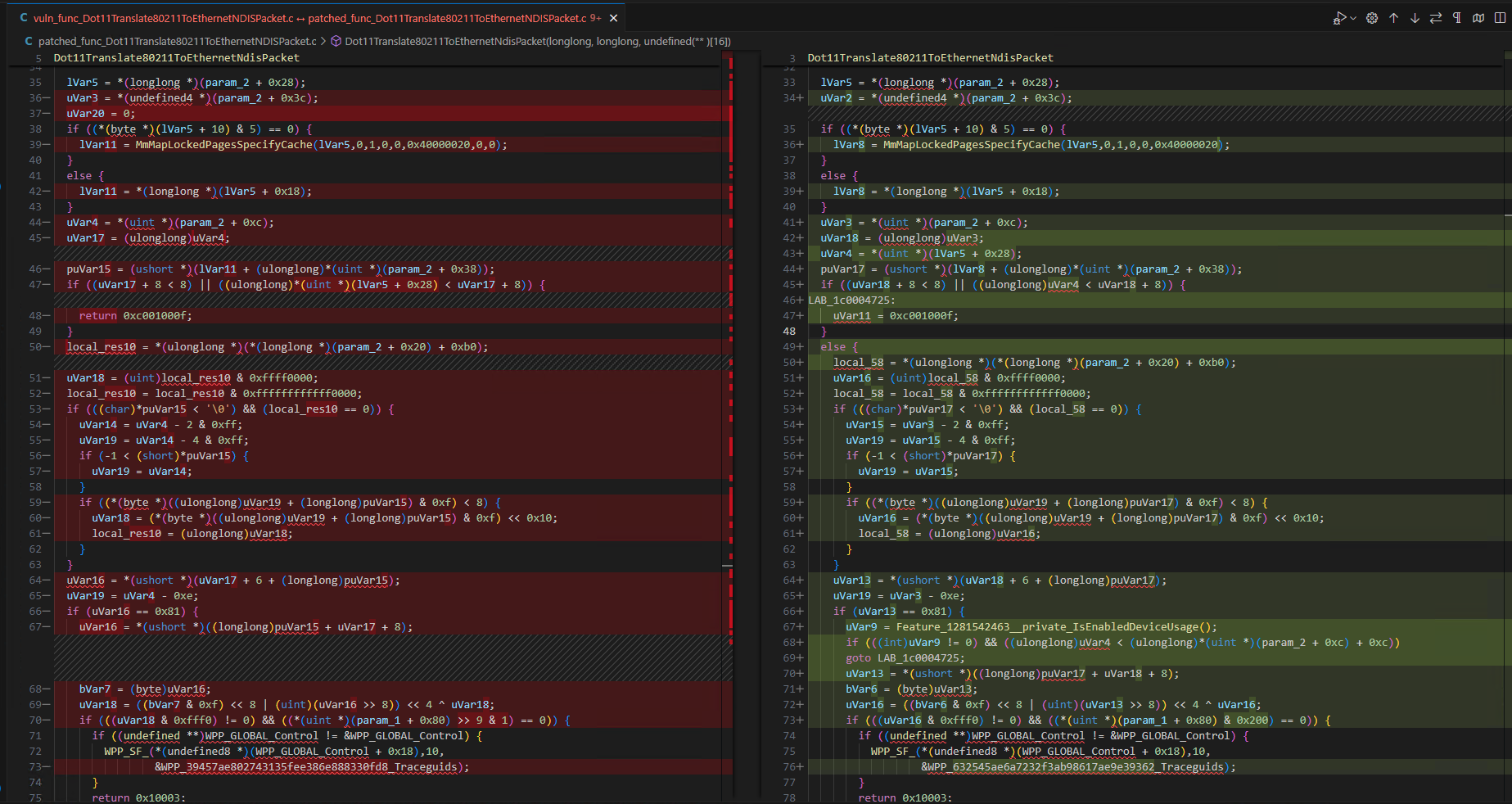
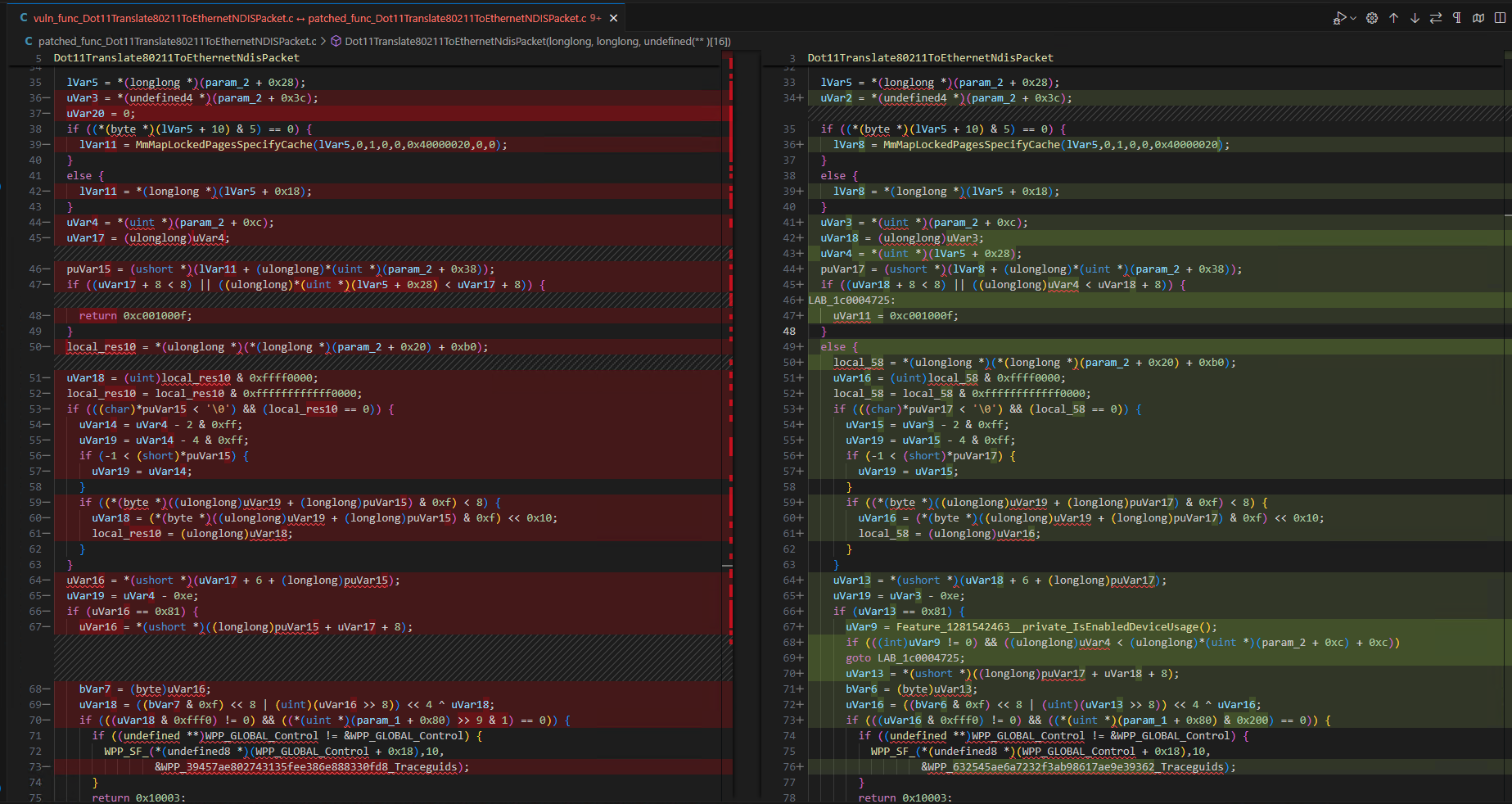
Analysing the Microsoft Windows Wi-Fi driver patch to understand the vulnerability (CVE-2024-30078) - Part2
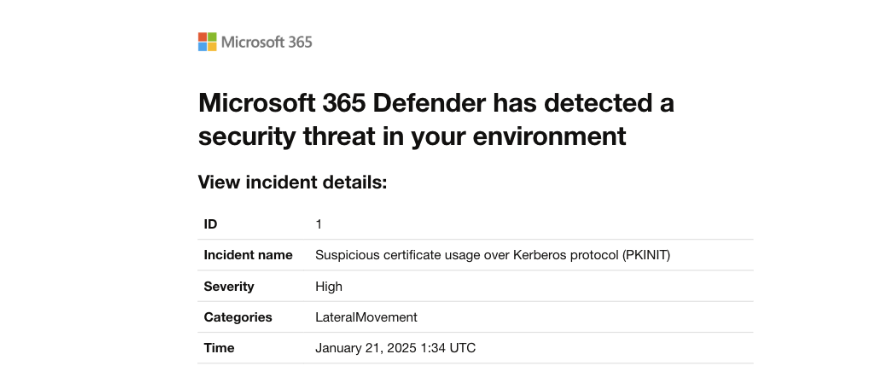
Bypassing Microsoft Defender for Identity Suspicious certificate usage over Kerberos protocol (PKINIT) high severity alert.
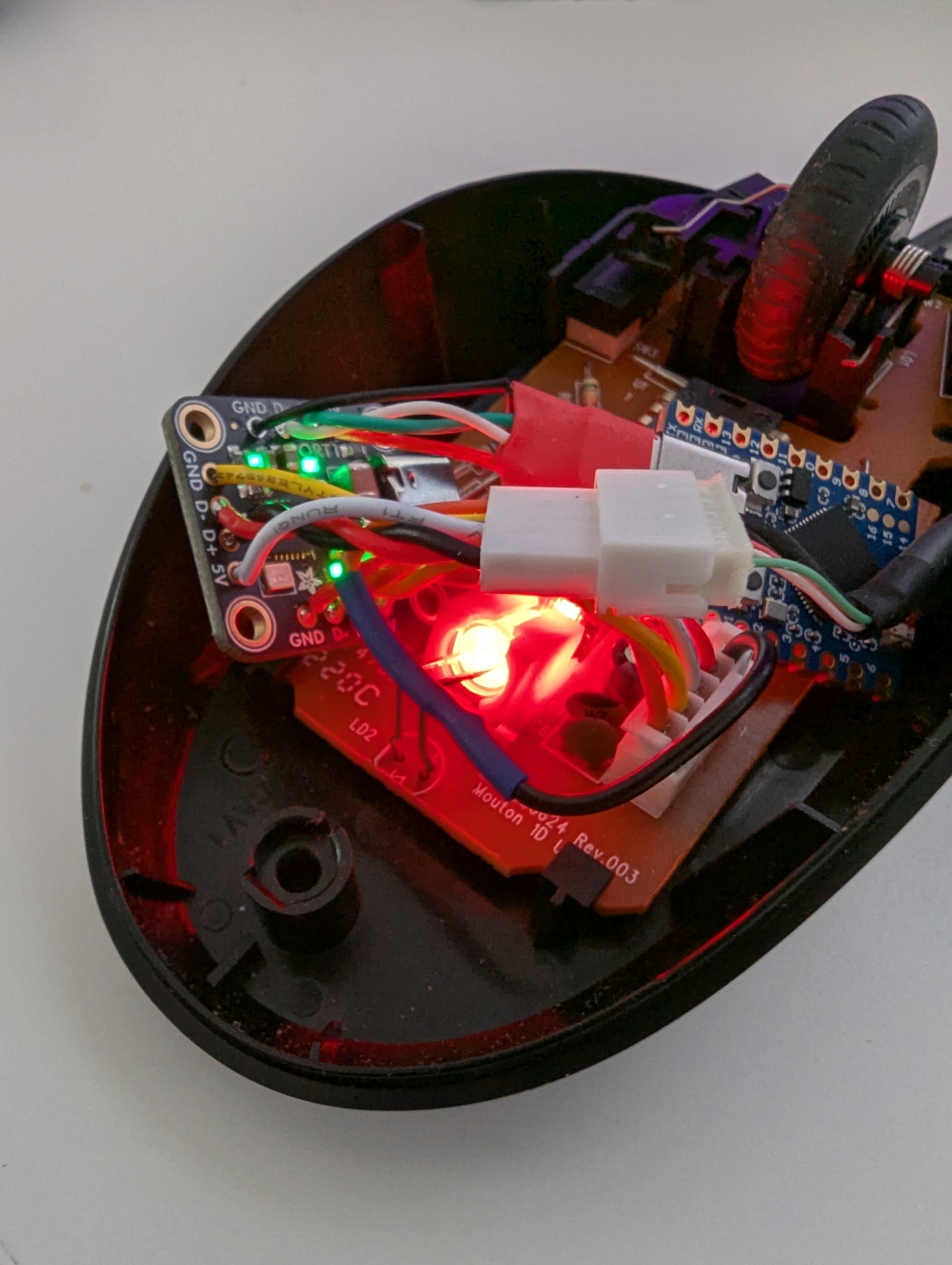
A quick post about making a more cost effective cover implant using a common wired mouse.
Analysing the Microsoft Windows Wi-Fi driver patch to understand the vulnerability (CVE-2024-30078) - Part1
Bypassing security prompts with file shares and more
Explore how GitHub Actions can be leveraged to rotate IP addresses during password spraying attacks to bypass IP-Based blocking such as Entra Smart lockout.
A detailed walkthrough of the process and hurdles faced in leveraging Evilginx3 to conduct a successful phishing campaign on a AD FS protected domain.
CVE-2023-35803 - An adventure in finding and exploiting a buffer overflow in Extreme Networks/Aerohive Wireless Access Points